365 Technologies: Blog
Technology provides a competitive advantage when implemented properly. Keeping up with the latest trends is not easy. On this page we will provide you with unbiased answers to common questions we receive. This will ensure you get the information you are looking for to make sound decisions. If there is something that you would like answers to, but do not see it below, let us know and we will add it.
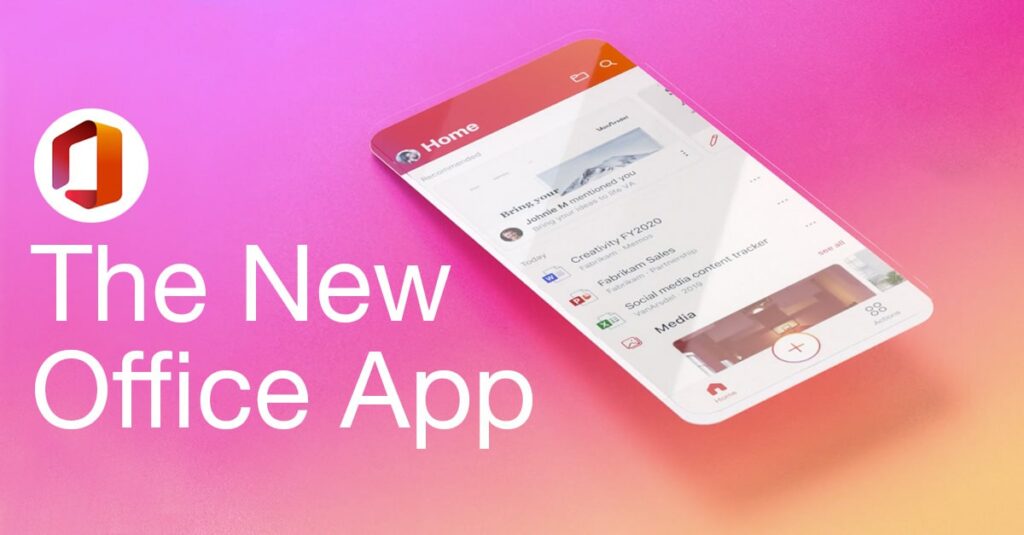
The new Microsoft Office app is “pretty great”
One app is better than three. In February, Microsoft released an updated Office app available for Android and iOS. The new app combines Word, Excel, and PowerPoint into a single download with new capabilities that enable you to create content…
Read MoreTech Tips: Microsoft Teams Keyboard Shortcuts
365 Technologies Tech Tips In this training tutorial, we show you how to access Microsoft Teams “keyboard shortcuts” and useful shortcut keys to help you navigate the interface quickly and make you Microsoft Teams pro. We provide Worry-Free IT™ for…
Read MoreCybersecurity tips for remote workers
Moving to a home office can be overwhelming and create cybersecurity issues for you, your team and organization – particularly on short notice! Here are some tips to make your home office and organization more secure: Virtual Private Network (VPN):…
Read MoreMicrosoft Teams Quick User Guides
Quick guides to help you set up remotely To help you, your team, and organization set up quickly with Microsoft Teams, here are some useful quick guides for you to download and share: Teams Meetings Quick Start Guide Teams App…
Read MoreA Crash Course in Microsoft Teams
Microsoft Teams with Michael Anderson With more organizations working remotely because of COVID-19, we thought we’d put out a quick Microsoft Teams crash course to help you navigate the system. In this short training video, Michael Anderson, our President &…
Read MoreRecent Posts
How can we help?
Whether you need immediate help with an IT issue or want to discuss your long-term IT strategy, our team is here to help.
Call us at (204) 336-6518 or complete the form below and we'll help in any way we can.
Categories
- 365 News
- Business Talk
- Cloud
- Culture
- Cybersecurity
- Disaster Recovery
- eBooks
- Green Technology
- Hardware
- IT Best Practices
- IT Managed Services
- IT Security
- Microsoft 365
- Microsoft Bookings
- Microsoft Forms
- Microsoft OneDrive
- Microsoft Teams
- Ransomware
- Remote Working
- Software
- Tech Articles
- Video Library